6 Cyber Predictions for 2026
We asked directors Ewan Ferguson and Chris Templeton to look into their crystal balls and suggest what challenges might be facing the cyber security community in 2026. Here are their...

Why work with an F5 Gold Partner?
When your infrastructure depends on secure, high-performing applications, choosing the right partner to deploy, optimise and support an F5 environment can make a world of difference. But with a wide...

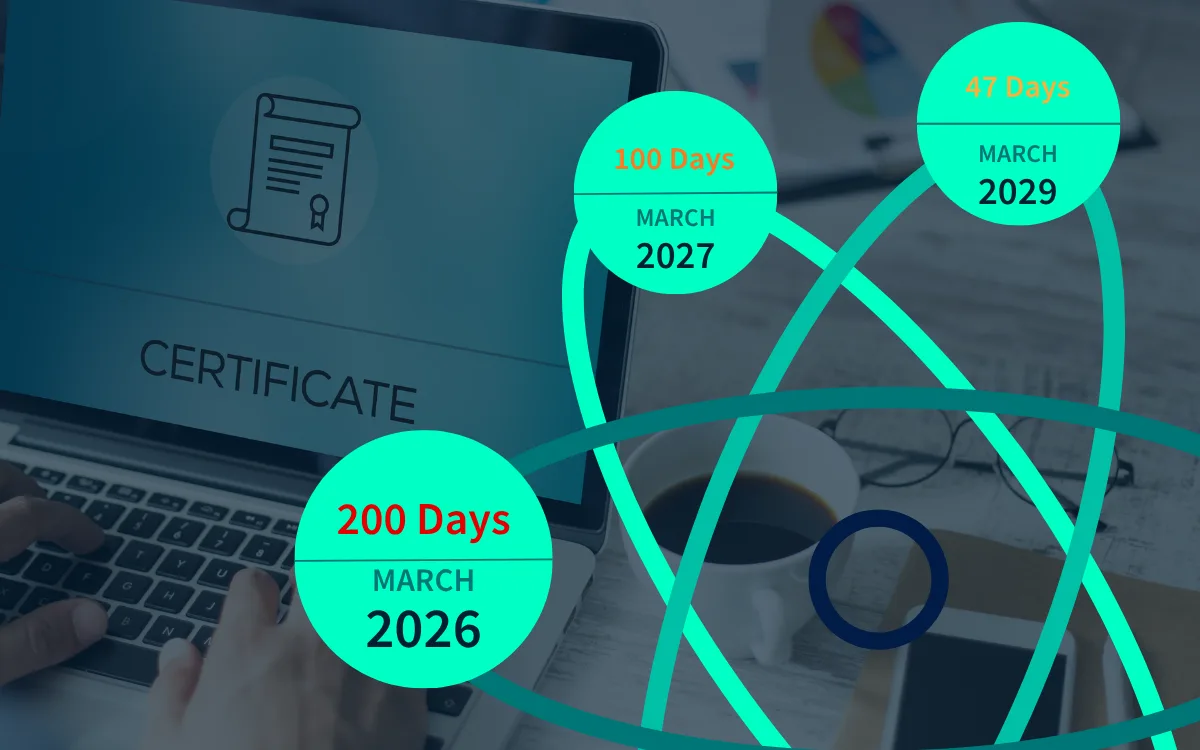
Are you ready for the 200-Day TLS Certificate Change? What You Need to Know
From March 2026, the security and IT operations world will experience a major shift - the maximum validity period for public TLS/SSL certificates is being cut from around 398 days...
Will Upgrading to F5 rSeries Improve my Quantum Resilience?
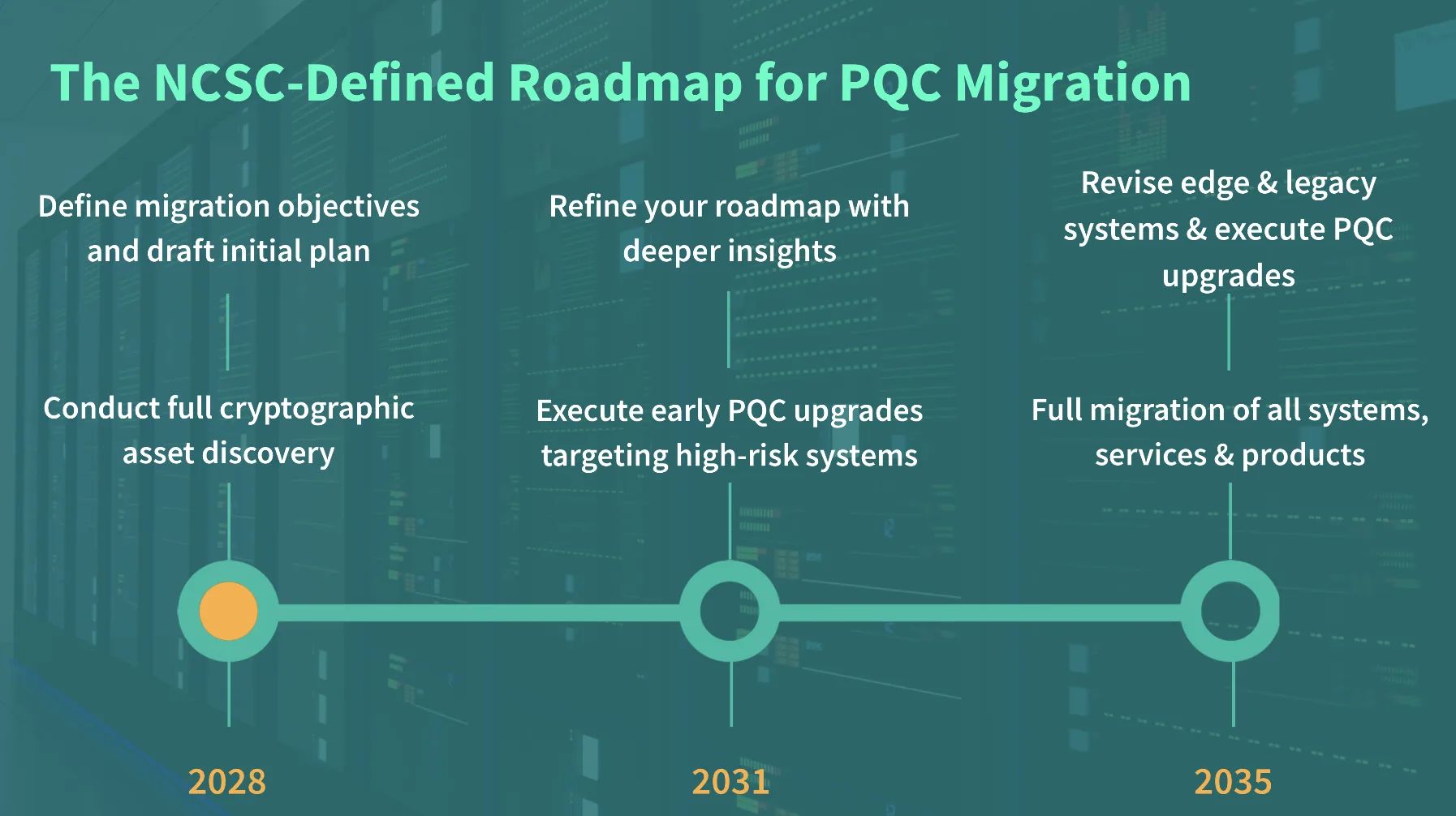
When sufficiently powerful machines arrive, today’s encryption standards - RSA, ECC, and others - will be rendered obsolete. The UK’s National Cyber Security Centre (NCSC) has already set a 2028...

Crypto-Agility explained; why you need it before 2028
Crypto-agility is your organisation’s ability to quickly adapt to new cryptographic standards without disrupting business operations. Today, most organisations rely on fixed algorithms like RSA or ECC....

PQC Timeline: do I really need to start now?
The NCSC has published its Post-Quantum Cryptography timeline. Learn why 2028 isn’t as far away as it looks and what steps to take now to prepare....